Missed alerts turn into outages, outages turn into lost revenue. ExterNetworks Inc. delivers 24/7 NOC & Help Desk support to keep everything running smoothly.
Get 24/7 IT Support NowEvery organization faces threats from ransomware attacks, insider breaches, and physical theft. Security controls are safeguards and countermeasures put in place to protect information systems, data, and physical assets against threats. Think of them as the locks, cameras, policies, and processes that collectively keep an organization’s operations secure.
According to PurpleSec, security controls are designed to preserve confidentiality, integrity, and availability — the CIA triad that underpins nearly every security decision a team makes. Whether you’re protecting a small business network or enterprise infrastructure, these controls form the backbone of a resilient security posture.
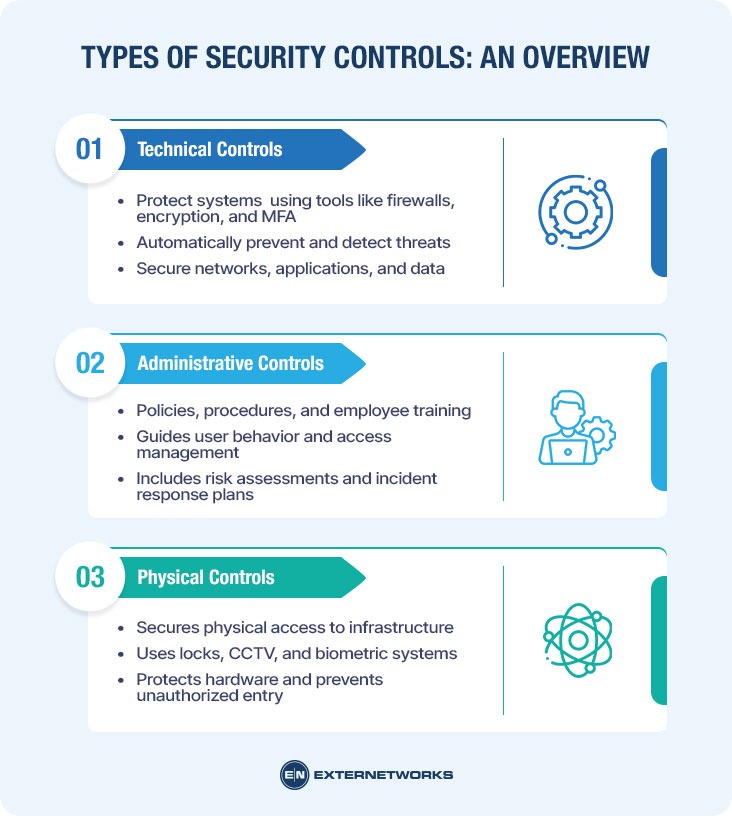
Security controls are not one-size-fits-all — they span technical, administrative, and physical categories, each serving a distinct purpose. Before diving into those categories, it helps to understand a few foundational concepts that make the whole framework click.
Before diving into the different types of security controls, it helps to have a clear foundation. Think of security controls as the building blocks of any solid defense strategy—but like any construction project, the quality of your foundation determines how well everything else holds up.
A few core concepts worth understanding upfront:
Understanding how access permissions work across systems is also essential groundwork, since many controls revolve around restricting who can do what. According to CyCognito, effective security controls must align with an organization’s specific risk profile—not just industry defaults.
Security controls are effective only when matched to real threats. With these concepts in place, exploring the full landscape of control types becomes much more intuitive.
Now that you’ve got the foundational concepts down, it’s time to map out the landscape. Cybersecurity controls don’t come in a one-size-fits-all package—they’re organized into distinct categories, each serving a specific role in your overall defense strategy.
According to PurpleSec, security controls break down into three primary types based on how they protect assets:
A practical way to think about it: no single category is sufficient alone—effective security demands layering all three. A robust firewall is ineffective if employees are not trained to spot phishing emails, and strong policies fall flat without enforced network-level protections.
Each category also operates across different functional modes—preventing, detecting, or responding to threats. Understanding that distinction is exactly where we’re headed next.
Technical controls are the technology-based safeguards that directly protect systems, networks, and data. Think of them as the digital locks, alarms, and surveillance cameras of your cybersecurity infrastructure. They operate automatically, enforcing security policies without requiring manual intervention whenever a threat arises.
Common examples include:
According to PurpleSec, technical controls span both preventive and detective functions — a single well-configured system can stop threats and flag anomalies simultaneously.
Strong technical controls are effective only with proper governing policies. That’s where administrative controls come in — shaping the human decisions and organizational procedures that technical tools alone can’t address.
While technical controls handle the digital heavy lifting, administrative controls form the organizational backbone of any security program. These are the human-facing safeguards — policies, procedures, training programs, and governance frameworks — that guide how people behave within a system.
Think of administrative controls as the rulebook everyone must follow. They include:
According to PurpleSec, administrative controls are often where security programs succeed or fail — technical investments cannot compensate for poorly trained staff or inconsistent policy enforcement.
Understanding how policies differ from controls is also valuable here: policies state what must happen, while controls ensure those requirements are actually met.
Up next, we’ll step away from screens and examine the often-overlooked world of physical controls.
While technical and administrative controls guard the digital realm, physical controls secure the tangible world where your infrastructure actually lives. These safeguards govern who can physically access servers, data centers, networking equipment, and other critical hardware — because even the most sophisticated firewall can’t stop someone from walking out with a hard drive.
Common physical controls include:
In practice, physical and digital threats are deeply intertwined. A breach in physical security can compromise all deployed technical controls — particularly in environments that rely on traditional perimeter-based security models, where physical boundaries carry significant trust assumptions.
Physical controls are only as strong as the policies enforcing them — making them a natural bridge between the layers we’ve explored so far and the practical implementation strategies coming up next.
Knowing the types of security controls is only half the battle — deploying them effectively is what actually reduces risk. A well-rounded implementation strategy layers preventive controls alongside detective and corrective measures, ensuring that threats are blocked before they cause damage and that they are caught quickly when they slip through.
One practical approach is to follow a defense-in-depth model. Rather than relying on a single control, stack multiple layers across technical, administrative, and physical domains (as covered in earlier sections). This way, if one control fails, another picks up the slack.
A few implementation best practices worth following:
Effective security controls don’t live in isolation — they work as a coordinated system, continuously refined through testing, feedback, and changing threat intelligence.
Consistent implementation also means regularly revisiting controls. Threats evolve, and a control that was sufficient last year may be inadequate today. That raises an important question: how do you know whether your controls are actually working? That’s exactly what evaluating control effectiveness is all about.
Deploying security controls is a meaningful achievement — but knowing whether they’re actually working is what separates a proactive security program from a false sense of security. Regular evaluation keeps your defenses honest.
A practical starting point is measuring each control against its intended purpose. Detective controls, for example, should be assessed by how quickly and accurately they identify anomalies or incidents. If an intrusion detection system generates too many false positives — or worse, misses real threats — it needs tuning, not just documentation.
Key evaluation methods include:
Strong controls don’t just exist on paper — they demonstrate measurable, repeatable results under real-world conditions. According to PurpleSec, layering control types ensures that when one fails, others compensate.
For organizations leveraging outsourced IT security support, continuous monitoring and reporting can make this evaluation process significantly more systematic. Of course, even the best evaluation programs encounter real-world obstacles, which brings us to the common challenges organizations face when managing security controls at scale.
Even a well-designed security control framework runs into real-world friction. Understanding these hurdles upfront helps teams avoid costly missteps.
Complexity and resource constraints are among the most common obstacles. Smaller organizations often struggle to implement and maintain layered controls without dedicated security staff. In practice, teams may deprioritize corrective controls — the mechanisms that restore systems after an incident — simply because they’re focused on prevention and detection. That’s a dangerous gap: without strong corrective capabilities, even the best preventive setup can leave an organization slow to recover when breaches occur.
Alert fatigue is another persistent challenge. Overly sensitive detective controls can flood teams with false positives, burying genuine threats in noise.
It’s also worth acknowledging that no control is foolproof. Controls can become outdated as threat landscapes evolve, particularly in complex environments like virtualized infrastructure, where attack surfaces shift constantly.
Security controls are only as strong as the processes and people supporting them — technology alone can’t compensate for poor governance or undertrained staff.
Balancing thoroughness with operational efficiency remains an ongoing challenge. These considerations set the stage for seeing how real organizations navigate them across different industries.
Seeing security controls applied across real-world industries makes their purpose far more tangible. Different sectors face unique threat landscapes — and their control strategies reflect that.
Healthcare organizations prioritize protecting patient data under HIPAA. In practice, this means encrypting electronic health records, enforcing role-based access controls, and deploying deterrent controls such as prominent audit-logging notices that discourage insider misuse before it starts.
Financial services firms layer compensating controls aggressively. Multi-factor authentication, transaction monitoring, and strict session timeouts work together to protect high-value assets around the clock. Many institutions rely on continuous monitoring workflows to catch anomalies in real time.
Retail and e-commerce environments rely heavily on PCI-DSS frameworks, combining preventive controls (tokenization, network segmentation) with detective controls such as intrusion detection systems.
Government and critical infrastructure sectors follow NIST SP 800-53, applying controls across the physical, operational, and technical domains simultaneously — often with rigorous structured oversight processes that ensure controls are consistently reviewed and updated.
A well-chosen set of industry-specific controls doesn’t just check compliance boxes — it builds a defensible security posture that fits the actual threat environment.
The patterns across these industries reinforce everything covered so far, pointing toward a few core principles worth carrying forward.
Security controls are the backbone of any effective cybersecurity strategy. Here’s a quick recap of what matters most:
As PurpleSec aptly notes, understanding which control type addresses which threat is what separates reactive security from truly strategic defense. The information and frameworks referenced throughout this article provide a strong foundation for building that understanding.
The information in this article draws on well-established cybersecurity resources to ensure accuracy and depth. For further reading on security controls, their types, and implementation frameworks, the following sources are recommended:
These resources offer authoritative perspectives on security control classifications, compliance frameworks, and practical implementation guidance. Consulting primary sources directly is always recommended when building or auditing a security program.
See how ExterNetworks can help you with Managed NOC Services
Contact Us