Missed alerts turn into outages, outages turn into lost revenue. ExterNetworks Inc. delivers 24/7 NOC & Help Desk support to keep everything running smoothly.
Get 24/7 IT Support NowA stateful firewall is one of the most intelligent tools in modern network security — and understanding how it works is essential for anyone responsible for protecting networked systems. Unlike basic packet filters that evaluate each data packet in isolation, a stateful firewall tracks the context of every network connection, making far smarter decisions about what traffic to allow or block.
At the heart of this technology is the state table firewall mechanism—a dynamic table that logs connection details, such as source and destination IP addresses, port numbers, and the current state of each session. Every packet is evaluated not just on its own merit, but against the history of the conversation it belongs to. As Palo Alto Networks explains, stateful inspection allows a firewall to determine whether a packet legitimately belongs to an established connection.
A stateful firewall doesn’t just filter traffic — it understands it, treating each packet as part of an ongoing dialogue rather than a standalone event.
Before diving deeper into how stateful firewalls work, it’s worth grounding that knowledge in core network security fundamentals.
Before diving deeper into how a stateful inspection firewall functions, it helps to establish a few foundational concepts — particularly for readers building their security knowledge from the ground up.
At its core, network security involves protecting data as it travels between devices, servers, and external networks. Every connection your system makes follows a defined protocol — most commonly TCP/IP — and each data exchange is broken into discrete packets. Understanding how packets work is essential because firewalls operate at this level, inspecting each packet before deciding whether to allow or block it.
Two key ideas matter here:
Any meaningful firewall comparison starts with recognizing that not all firewalls handle these two elements the same way. Some only examine individual packets in isolation; others track the full context of a session. That distinction — context versus no context — is precisely what separates more capable security tools from basic ones.
Maintaining a solid baseline security posture is what makes these distinctions matter in real-world environments. With that groundwork in place, we can examine exactly how stateful firewalls track and evaluate network traffic at every stage of a connection.
At its core, a stateful inspection firewall tracks the full lifecycle of every network connection — not just evaluating individual packets in isolation. This distinction is what separates it from simpler, stateless approaches.
When a connection is initiated, the firewall records key session details in a state table (also called a connection tracking table). According to Check Point, this table stores attributes, including:
Every subsequent packet belonging to that session is matched against this state table. If a packet aligns with a known, active connection, it passes through. If it doesn’t match any legitimate session — or arrives out of sequence — the firewall drops it.
What makes this powerful is context. As Paubox notes, the firewall dynamically updates its state table in real time, adapting to the evolving status of each connection. This means it can detect anomalies that a packet-by-packet inspection would miss entirely.
In practice, this also means stateful firewalls integrate naturally into broader monitoring strategies — something worth considering when reviewing your overall network visibility approach.
Understanding how this operates logically raises an important follow-up question: what specific components make this state-tracking mechanism work? That’s exactly what the next section breaks down.
A stateful firewall is more than just a filter — it’s a sophisticated network security device built from several interconnected components that work together to enforce intelligent traffic decisions. Understanding what’s under the hood helps clarify why this architecture outperforms simpler alternatives.
The state table is the engine of the entire system. Also called the connection tracking table, it records key session attributes for every active connection, including:
As ConnectWise explains, this dynamic table is continuously updated with each passing packet, giving the firewall a real-time view of network activity rather than a static snapshot.
The packet inspection engine evaluates incoming data against both predefined rules and live state table entries. If a packet matches an existing, legitimate session, it is allowed to pass. If it doesn’t align with any known connection context, it’s flagged or dropped.
Supporting these components is a rule—based policy layer that defines what traffic is permitted or denied. Think of it as the decision framework the inspection engine consults on every judgment call. For a broader look at how firewalls are categorized by design, these components appear across multiple firewall types in varying configurations.
Together, these elements make stateful firewalls remarkably precise — a quality that becomes even clearer when you see them applied to real-world traffic scenarios.
Understanding how a connection-tracking firewall works becomes much clearer with a real-world example. Think of a stateful firewall like a security guard at a gated office building — one who doesn’t just check IDs at the door, but actively logs every visitor, tracks where they’re headed, and verifies they leave through the proper exit.
When a visitor (a data packet) arrives, the guard notes their name, destination, arrival time, and purpose. If someone tries to enter without a matching record — or claims to be leaving when they never signed in — the guard flags the anomaly immediately. A stateful firewall applies this same contextual logic to every packet crossing your network.
In practice, when your browser requests a webpage, the firewall logs that outbound request. When the server responds, the firewall validates that the incoming traffic matches the original session — not just the port or IP, but the full connection context. Packets that don’t align with a known session are automatically blocked.
This is precisely why stateful inspection outperforms rule-based alternatives: context matters. Knowing how your network infrastructure components interact helps illustrate why tracking connection state — rather than inspecting packets individually — is fundamentally more secure, as Huntress notes in their cybersecurity overview.
The analogy sets the stage for understanding how these protections play out in real deployment scenarios.
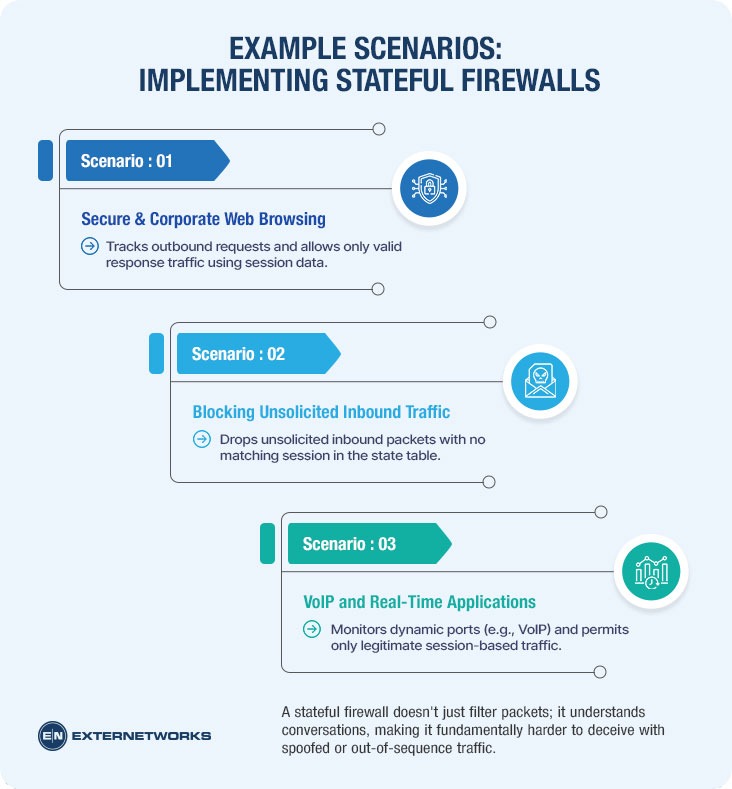
Seeing how stateful firewalls operate in real environments helps bridge the gap between theory and practice. The following scenarios illustrate where stateful inspection delivers clear, measurable value—and where the stateless vs. stateful firewall distinction becomes especially relevant.
Scenario 1: Corporate Web Browsing An employee opens a browser and requests a page from an external website. The firewall logs the outbound TCP connection in its state table. When the web server’s response packets arrive, the firewall recognizes them as part of an established session and automatically permits them — no manual inbound rule required.
Scenario 2: Blocking Unsolicited Inbound Traffic An attacker sends unsolicited packets to an internal IP address. Because no matching entry exists in the state table, the firewall silently drops them. This behavior is a core reason stateful firewalls are standard in protecting business environments.
Scenario 3: VoIP and Real-Time Applications. For protocols like SIP, the firewall tracks dynamic port negotiations, allowing media streams only when they correspond to a logged session — preventing unauthorized channel abuse.
A stateful firewall doesn’t just filter packets; it understands conversations, making it fundamentally harder to deceive with spoofed or out-of-sequence traffic.
In practice, these behaviors depend entirely on accurate state tracking, which leads naturally into how stateful packet inspection works at the technical level.
At the core of every stateful firewall lies stateful packet inspection (SPI) — the mechanism that enables context-aware filtering. Unlike basic packet filtering, which evaluates each packet independently, SPI tracks the full lifecycle of a network connection.
The firewall maintains a state table (also called a connection tracking table) that dynamically records key attributes for every active session:
Each incoming and outgoing packet is matched against this table. If a packet belongs to a known, legitimate session, it’s allowed through. If it doesn’t match any active entry—or arrives out of sequence—the firewall flags or drops it. According to NIST guidelines on firewall policy, this connection-level awareness is a defining advantage over earlier filtering methods.
Stateful packet inspection prevents spoofed packets from hijacking active sessions by verifying that TCP sequence numbers align with the established connection — a check no stateless approach can perform.
This granularity also supports stronger endpoint protection by ensuring only legitimate, tracked traffic reaches internal resources.
As the scenarios covered earlier demonstrate, SPI is what separates intelligent filtering from simple rule-matching — and understanding its limits is equally important, which naturally leads to evaluating the trade-offs stateful firewalls entail.
Stateful firewalls offer significant advantages, but no security tool is without limitations. Understanding where they fall short helps organizations make smarter decisions about layering defenses appropriately.
Key limitations to consider:
Alternatives and complementary tools worth evaluating include:
A stateful firewall alone is never a complete security strategy — it functions best as one layer within a broader, defense-in-depth architecture. Pairing it with robust traffic monitoring capabilities strengthens your ability to detect threats that inspection alone misses.
With these trade-offs in mind, examining how large enterprises navigate these decisions in practice reveals valuable lessons about real-world implementation.
To see stateful firewalls in action, consider a common scenario in large enterprise environments. A financial services organization with thousands of endpoints and multiple branch offices needs to enforce strict access controls while maintaining seamless connectivity for legitimate business traffic.
Example scenario: The organization deploys stateful firewalls at each network perimeter, replacing older packet-filtering solutions. Network engineers configure the state table to track all outbound connections initiated by internal users. When responses arrive, the firewall validates each packet against its recorded session data — source IP, destination port, and sequence numbers — before allowing it to enter. Unsolicited inbound packets are dropped automatically.
The immediate difference between stateful inspection and stateless approaches becomes clear during a port-scan attempt. Where a stateless filter might pass crafted packets that match simple rule criteria, a stateful firewall identifies them as lacking a corresponding session entry and blocks them outright.
Effective ongoing management is equally critical. Teams responsible for keeping the network running smoothly regularly monitor state table capacity and connection timeouts, ensuring performance doesn’t degrade under heavy load. As risk3sixty notes, consistent policy review and log analysis are what separate a well-tuned stateful firewall from one that merely exists on the network. These operational habits — not just the technology itself — define how much protection an organization actually gains, a principle worth carrying into any broader security evaluation.
Understanding what a stateful firewall is — and how it works — is foundational knowledge for anyone responsible for protecting a modern network. Unlike basic packet filters, a stateful firewall tracks the full context of every connection, making intelligent decisions based on traffic history rather than isolated packet data. That context-awareness is what separates it from simpler alternatives.
Here’s a quick summary of what this guide covered:
A well-configured stateful inspection firewall remains one of the most reliable first lines of defense available today. As threats evolve, pairing it with complementary tools — next-generation capabilities, intrusion detection, and zero-trust principles — ensures your security posture keeps pace. Start by auditing your current firewall configuration, and build from there.
See how ExterNetworks can help you with Managed NOC Services
Contact Us