Missed alerts turn into outages, outages turn into lost revenue. ExterNetworks Inc. delivers 24/7 NOC & Help Desk support to keep everything running smoothly.
Get 24/7 IT Support NowThe average cost of a data breach in the United States has shattered records — and in 2026, no organization is immune. When a single security failure can paralyze operations, erode customer trust, and trigger regulatory penalties simultaneously, treating data center security as a line-item expense is no longer just shortsighted. It’s existential.
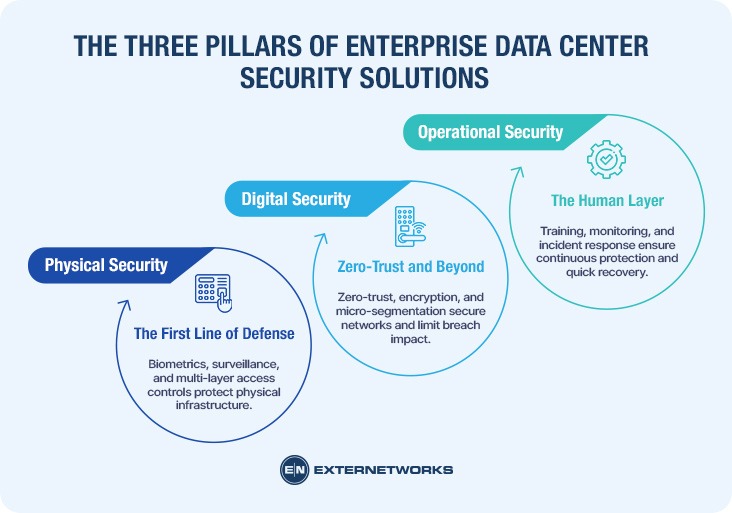
Data center security is no longer a single-layer problem. It’s a multi-layered discipline spanning three interconnected domains: physical controls that protect hardware and facilities, digital defenses that guard networks and data, and operational protocols that govern human behavior and incident response. Weakness in any one domain creates a vulnerability that attackers — or simple human error — will inevitably exploit.
Here’s the critical shift happening right now: forward-thinking enterprises are reframing security as a business enabler rather than a cost center. Investing in managed data center security services doesn’t just reduce risk — it builds the operational credibility that wins enterprise contracts, satisfies auditors, and accelerates growth.
The thesis is straightforward: integration is the only path to resilience. A patchwork of disconnected tools creates gaps. A unified, layered strategy closes them. Understanding exactly how that strategy is built starts with the three pillars on which every enterprise security framework depends.
Understanding why data breaches cost organizations millions starts with understanding how they happen—and, more importantly, what stops them. The most effective enterprise data center security solutions aren’t built around a single defensive layer. They’re structured around three interconnected pillars, each reinforcing the others.
Physical security has evolved far beyond locked server room doors. Modern facilities deploy biometric authentication, perimeter surveillance with AI-assisted threat detection, and multi-zone access controls that segment who can reach which areas of a facility. A data center employee might swipe a badge, scan a fingerprint, and pass through a mantrap — all before touching a single rack. This layered approach ensures that a stolen credential alone can’t grant physical access to critical infrastructure. The specifics of how leading facilities architect these defenses — from bollards to rack-level locking — deserve their own detailed treatment.
On the digital side, the shift away from perimeter-based security models is well underway. Broadcom’s enterprise security research makes clear that assuming everything inside a network is trusted is a dangerous legacy mindset. Leading facilities now implement zero-trust architecture, end-to-end encryption, and micro-segmentation — isolating workloads so that a breach in one segment can’t cascade across the environment. As Tigera notes, unified microsegmentation, when paired with observability, dramatically reduces the blast radius of any incident.
Technology alone doesn’t secure a data center — people and processes do. Operational security covers incident response protocols, staff training, access auditing, and continuous monitoring. A well-documented incident response plan is the difference between a contained breach and a headline-generating disaster. Tier 4 facilities — the gold standard in uptime and resilience — treat operational rigor as non-negotiable, running regular drills and maintaining 24/7 security operations centers.
Together, these three pillars create a defense-in-depth posture that transforms security from a cost center into a competitive advantage.
The three pillars covered in the previous section — physical controls, digital defenses, and operational protocols — don’t exist in isolation. Physical security is where abstract policy meets concrete reality, and getting it wrong creates vulnerabilities that no software patch can fix.
Effective data center security starts well before anyone reaches a server rack. A layered perimeter defense combines fencing, K-rated bollards (vehicle-rated barriers engineered to withstand multi-ton impacts), and thermal imaging cameras that detect heat signatures even in complete darkness. Each layer forces an attacker to slow down — and every additional second of dwell time increases detection probability.
The era of swipe-and-enter is over. Modern facilities are transitioning rapidly from single-factor keycards to multi-factor biometric authentication — combining fingerprint scans, iris recognition, and PIN codes at entry points. This shift matters because stolen credentials remain one of the most common attack vectors. Layering biometrics over traditional access cards means a lost badge alone can’t compromise a facility. As enterprise identity management practices evolve in 2025, the principle is clear: identity verification must be continuous, not a one-time checkpoint.
Inside the facility, mantraps — dual-door entry chambers that prevent tailgating — and rack-level locking are non-negotiable for any serious security posture. One open rack in an unsupervised aisle is all an insider threat needs.
Environmental security deserves equal weight. Fire suppression systems using clean-agent gases and flood mitigation barriers protect hardware that no amount of cybersecurity spending can replace once it’s destroyed.
Hardening physical infrastructure is foundational — but monitoring it continuously is where the real operational challenge lies. That’s where integrating NOC services for data centers becomes essential, bridging real-time environmental oversight with proactive threat detection.
Physical hardening and zero trust architecture establish a strong foundation — but who’s watching the dashboard at 3 a.m. when an anomaly surfaces? That’s where managed services, and specifically the integration of Network Operations Centers (NOC) and Security Operations Centers (SOC), become a decisive advantage.
These two functions are often conflated, but they serve distinct purposes. A NOC focuses on performance and availability — monitoring uptime, bandwidth, latency, and system health. A SOC is dedicated to threat detection, incident response, and vulnerability management. Effective security operation center data center management combines both disciplines so that a performance anomaly (a NOC concern) can be immediately cross-referenced against threat intelligence (a SOC concern). What appears to be a bandwidth spike might actually be data exfiltration in progress.
A common pattern in underprepared organizations is treating security as reactive — investigating after something breaks. Continuous monitoring flips that model. By correlating NOC and SOC data streams in real time, integrated teams can identify behavioral deviations before they escalate into full breaches.
Reducing Mean Time to Detect (MTTD) is one of the most measurable outcomes of this approach. Faster detection directly compresses the damage window — and the financial exposure that comes with it.
Building an in-house 24/7 SOC requires significant investment in staffing, tooling, and training. Outsourced managed security services give enterprises access to specialized talent and enterprise-grade tooling without the overhead burden.
In practice, this trade-off appeals strongly to mid-market enterprises that need enterprise-level vigilance but can’t justify the headcount.
Knowing who’s monitoring your environment is only part of the equation, however. The other piece is demonstrating — to regulators, partners, and customers — that your security posture meets recognized compliance standards.
Understanding data center security compliance standards isn’t optional — for most enterprises, it’s the price of doing business. Compliance frameworks translate abstract security principles into concrete, auditable requirements, giving customers and regulators a shared language for trust.
SOC 2 Type II goes beyond a point-in-time snapshot. It validates that security controls have operated effectively over an extended period — typically six to twelve months. ISO 27001 takes a complementary approach, certifying that an organization has built a systematic information security management system. Together, they represent the baseline expectation for any enterprise-grade facility.
A facility that holds both certifications signals operational discipline, not just good intentions.
Compliance requirements sharpen considerably depending on your sector:
Failing either standard can mean regulatory penalties, lost contracts, or both.
Regular third-party audits are what separate documented policies from proven practice. No internal review carries the same credibility as an independent assessment. On the infrastructure side, Tier 1 through Tier 4 classifications — established by the Uptime Institute — directly correlate with redundancy levels and uptime guarantees, which in turn influence which compliance regimes a facility can realistically support.
The compliance conversation doesn’t stop at the data center perimeter, though. How facilities communicate their standards to the broader community around them matters as much—a topic worth examining closely.
When enterprise data centers expand into new regions, local resistance often follows. Concerns about radiation, electromagnetic fields (EMF), and constant industrial noise are common — and almost always overblown. Understanding what data center security is, why it is important, and how modern facilities operate helps separate genuine concern from unfounded fear.
The reality is straightforward: data centers produce no meaningful radiation hazard. EMF emissions fall well within established safety thresholds, and modern acoustic engineering keeps operational noise levels comparable to those of a typical office park — far quieter than in manufacturing or logistics facilities.
Corporate responsibility has become a genuine differentiator. Leading operators are investing heavily in renewable energy, stormwater management, and transparent community communication programs.
A common pattern is that neighborhood opposition often dissolves once facilities open honest dialogue about their security and environmental practices. Transparent communication about physical safeguards, redundancy systems, and green initiatives consistently builds goodwill.
Ultimately, the strongest argument for community acceptance isn’t just environmental — it’s economic. Data centers bring high-paying jobs and infrastructure investment. Choosing the right security partner, as the next section explores, means finding an operator equally committed to that community trust.
Enterprise data center security is never a one-time purchase — it’s a living, multi-layered commitment that operates around the clock, across physical, digital, and regulatory dimensions simultaneously.
As covered throughout this article, the stakes are real. A single breach can exceed $10 million in total business impact when penalties, downtime, and reputational damage compound. Secure, compliant infrastructure doesn’t just protect assets — it accelerates growth by unlocking regulated markets, winning enterprise contracts, and building stakeholder trust that competitors can’t match.
The CISO’s evolving role reflects this shift: security is now a core business enabler, not merely a cost center.
Now is the time to act. Audit your current security posture honestly. Identify the gaps. Then choose a long-term partner—not just a vendor—who can scale alongside your ambitions.
See how ExterNetworks can help you with Managed NOC Services
Contact Us